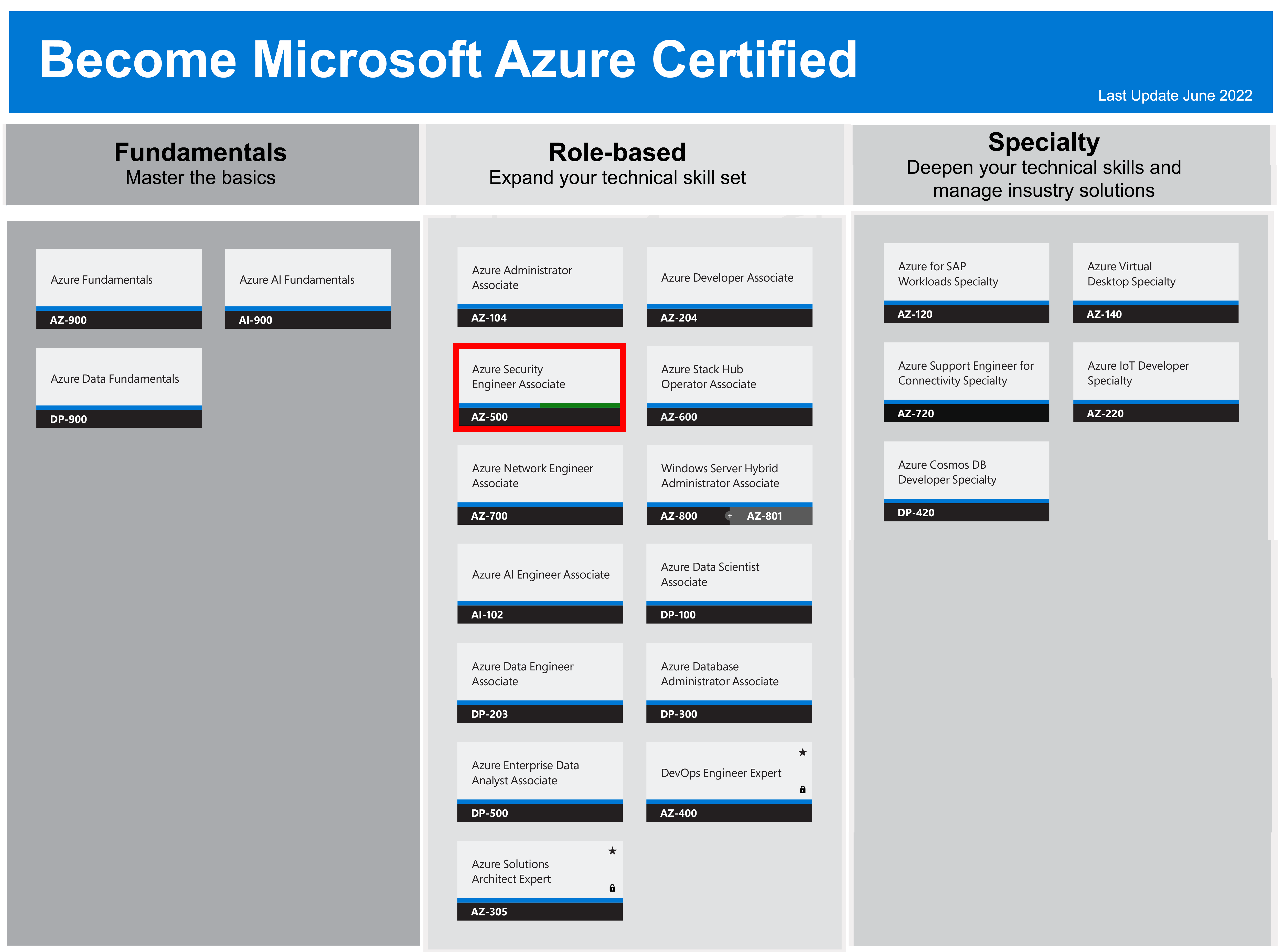
AZ-500 - Azure Security Engineer Associate
Microsoft cours officiels
Home » ISEIG Cours » AZ-500 – Azure Security Engineer Associate
Ce cours est dispensé en français sur la base d'une documentation pédagogique en anglais.
This course provides IT Security Professionals with the knowledge and skills needed to implement security controls, maintain an organization’s security posture, and identify and remediate security vulnerabilities. This course includes security for identity and access, platform protection, data and applications, and security operations.
These courses help prepare for the exam « Microsoft Azure Security Technologies (AZ-500) ».
This course provides IT Security Professionals with the knowledge and skills needed to implement security controls, maintain an organization’s security posture, and identify and remediate security vulnerabilities. This course includes security for identity and access, platform protection, data and applications, and security operations.
These courses help prepare for the exam « Microsoft Azure Security Technologies (AZ-500) ».
Modules et dates
This course of 4 days is given once a semester, 1 to 2 days a week, from 9:00 am to 12:00 pm and from 1:30 pm to 5:00 pm.
AZ-500 - Microsoft Azure Security Technologies
Durée
4
Prix
CHF 3'000.-
Prix/j.
CHF 750.-
Sur demande
These courses are given in French on the basis of documentation in French if available (Fra) or in English (Eng). If it is available in both languages, the French version is distributed unless specifically requested by the interested party. The price of the course includes all the pedagogical documentation distributed.
AZ-500 - Microsoft Azure Security Technologies
Overview
This course provides IT Security Professionals with the knowledge and skills needed to implement security controls, maintain an organization’s security posture, and identify and remediate security vulnerabilities. This course includes security for identity and access, platform protection, data and applications, and security operations.
Target Audience :
- This course provides IT Security Professionals with the knowledge and skills needed to implement security controls, maintain an organization’s security posture, and identify and remediate security vulnerabilities. This course includes security for identity and access, platform protection, data and applications, and security operations.
Objectives :
- implement enterprise governance strategies including role-based access control, Azure policies, and resource locks.
- implement an Azure AD infrastructure including users, groups, and multi-factor authentication.
- implement Azure AD Identity Protection including risk policies, conditional access, and access reviews.
- implement Azure AD Privileged Identity Management including Azure AD roles and Azure resources.
- implement Azure AD Connect including authentication methods and on-premises directory synchronization.
- implement perimeter security strategies including Azure Firewall.
- implement network security strategies including Network Security Groups and Application Security Groups.
- implement host security strategies including endpoint protection, remote access management, update management, and disk encryption.
- implement container security strategies including Azure Container Instances, Azure Container Registry, and Azure Kubernetes.
- implement Azure Key Vault including certificates, keys, and secretes.
- implement application security strategies including app registration, managed identities, and service endpoints.
- implement storage security strategies including shared access signatures, blob retention policies, and Azure Files authentication.
- implement database security strategies including authentication, data classification, dynamic data masking, and always encrypted.
- implement Azure Monitor including connected sources, log analytics, and alerts.
- implement Azure Security Center including policies, recommendations, and just in time virtual machine access.
- implement Azure Sentinel including workbooks, incidents, and playbooks.
Prerequisites :
Successful learners will have prior knowledge and understanding of:
- Security best practices and industry security requirements such as defense in depth, least privileged access, role-based access control, multi-factor authentication, shared responsibility, and zero trust model.
- Be familiar with security protocols such as Virtual Private Networks (VPN), Internet Security Protocol (IPSec), Secure Socket Layer (SSL), disk and data encryption methods.
- Have some experience deploying Azure workloads. This course does not cover the basics of Azure administration, instead the course content builds on that knowledge by adding security specific information.
- Have experience with Windows and Linux operating systems and scripting languages. Course labs may use PowerShell and the CLI.
Program :
This course is composed of 4 modules including lessons and practical work (lab)
- Manage Identity and Access
- Implement Platform Protection
- Secure Data and Applications
- Manage Security Operations
Module 1: Manage Identity and Access
This module covers Azure Active Directory, Azure Identity Protection, Enterprise Governance, Azure AD PIM, and Hybrid Identity.
Lesson:
This module covers perimeter, network, host, and container security.
Lesson:
This module covers Azure Key Vault, application security, storage security, and SQL database security.
Lesson:
This module covers Azure Monitor, Azure Security Center, and Azure Sentinel.
Lesson:
This module covers Azure Active Directory, Azure Identity Protection, Enterprise Governance, Azure AD PIM, and Hybrid Identity.
Lesson:
- Azure Active Directory
- Hybrid Identity
- Azure Identity Protection
- Azure AD Privileged Identity Management
- Enterprise Governance
- Role-Based Access ControlLab : Azure Policy
- Resource Manager Locks
- MFA, Conditional Access and AAD Identity Protection
- Azure AD Privileged Identity Management
- Implement Directory Synchronization
- Implement enterprise governance strategies including role-based access control, Azure policies, and resource locks.
- Implement an Azure AD infrastructure including users, groups, and multi-factor authentication.
- Implement Azure AD Identity Protection including risk policies, conditional access, and access reviews.
- Implement Azure AD Privileged Identity Management including Azure AD roles and Azure resources.
- Implement Azure AD Connect including authentication methods and on-premises directory synchronization.
This module covers perimeter, network, host, and container security.
Lesson:
- Perimeter Security
- Network Security
- Host Security
- Container Security
- Network Security Groups and Application Security Groups
- Azure FirewallLab : Configuring and Securing ACR and AKS
- Implement perimeter security strategies including Azure Firewall.
- Implement network security strategies including Network Security Groups and Application Security Groups.
- Implement host security strategies including endpoint protection, remote access management, update management, and disk encryption.
- Implement container security strategies including Azure Container Instances, Azure Container Registry, and Azure Kubernetes.
This module covers Azure Key Vault, application security, storage security, and SQL database security.
Lesson:
- Azure Key Vault
- Application Security
- Storage Security
- SQL Database Security
- Key Vault (Implementing Secure Data by setting up Always Encrypted)
- Securing Azure SQL DatabaseLab : Service Endpoints and Securing Storage
- Implement Azure Key Vault including certificates, keys, and secretes.
- Implement application security strategies including app registration, managed identities, and service endpoints.
- Implement storage security strategies including shared access signatures, blob retention policies, and Azure Files authentication.
- Implement database security strategies including authentication, data classification, dynamic data masking, and always encrypted.
This module covers Azure Monitor, Azure Security Center, and Azure Sentinel.
Lesson:
- Azure Monitor
- Azure Security Center
- Azure Sentinel
- Azure Monitor
- Azure Security Center
- Azure Sentinel
- Implement Azure Monitor including connected sources, log analytics, and alerts.
- Implement Azure Security Center including policies, recommendations, and just in time virtual machine access.
- Implement Azure Sentinel including workbooks, incidents, and playbooks.